What’s your password?
The question makes most of us cringe because we all have a gazillion passwords for banking, shopping and everything else we do online.
But with a passkey, there’s nothing to remember or type in. Touching our finger or showing our face to a device for authentication is so much easier.
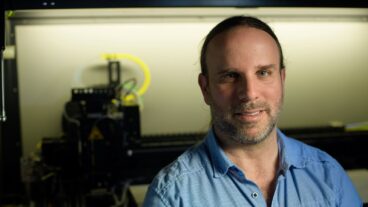
And it is safer, too, says Tal Zamir, CTO of Tel Aviv-based Perception Point, whose software detects, investigates and remediates any kind of hack attack across a company’s email, web browsers and cloud collaboration channels.
“Google’s recent decision to phase out passwords and replace them with passkeys is an important and necessary step in the right direction,” Zamir tells ISRAEL21c.

“The move is in response to the growing sophistication of phishing and credential theft attacks, which are becoming increasingly common in today’s digital landscape,” he explains.
“By requiring a physical passkey, Google hopes to make it much harder for attackers to steal user sessions, even if they have managed to steal passwords and second-factor authentication codes.”
But, though passkeys might be easier and safer than passwords, they are not the answer to all our problems, says Zamir.
The problem with passwords
“The main problem with passwords is that people forget them,” Zamir says.
Many try to avoid that problem by using the same password for different sites. But that just creates another problem: A hacker who steals the password now has access to more than one account.
Stealing passwords and personal identities has gotten easier as phishing techniques have gotten more sophisticated, he says. Perception Point has identified a 356% increase in advanced phishing attacks over the past year.
One solution is two-factor (or multifactor) authentication, where in addition to a password you need a code sent via SMS.
“Although it’s more secure than only a password, it’s still a problem because when you get a text on your phone or some other way, attackers can steal both your password and your second-factor authentication. They can also convince the cellular phone provider to hand over your number to an attacker, who gets the text message in your name,” says Zamir.
“This is happening every day. Passwords and second-factor authentication don’t really solve the problem of identity theft.”
Secure, user-friendly
This is why Microsoft, Apple and Google have been working with a consortium of companies toward a more secure and user-friendly authentication method, says Zamir.
“It’s rare that you see all these tech giants working together on an initiative, and that’s the key to its potential success,” he says.
“In this new world, there won’t be passwords, just biometric data. When you want to authenticate with some application or website, all you have to do is unlock your phone or other device with your fingerprint or face ID and that’s it. The computer or phone logs you in and holds all your secrets of authentication.”

Based on cryptography, passkeys are safe, easy, error-proof (unlike passwords) and phishing-resistant because you do not have a password or code for anyone to steal.
We’re already able to use passkeys on our devices, for example when signing into Google or making a purchase with Apple Pay.
Zamir predicts it will take another five to 10 years before every organization switches over to passkeys.
“Unfortunately, for the foreseeable future there are still secrets you can share with attackers,” says Zamir.
The catch
When passkeys do become widespread, they will reduce traditional phishing attacks but cannot completely prevent security breaches and identity theft.
“Unfortunately, for the foreseeable future there are still secrets you can share with attackers.”
For example, if your device is misplaced you will need a “recovery code” to prove your identity. Getting a code will require – you guessed it — a password or two-factor authentication that can be stolen.
“Phishing will simply move into the realm of stealing your recovery code instead of your password. We already see attackers doing this today. Once attackers gain access to your recovery code, they will immediately get access to all your accounts because the passkey is a master key to the secrets on your device.”
Nor can passkeys protect against “social-engineering” attacks that take advantage of human, not cyber, weakness.
These attacks don’t try to take over your account or steal your identity. They simply use an authentic-looking message, purportedly from a person or company you trust, instructing you to transfer funds or take some other harmful action.
“I’m not asking for a password, I’m just posing as a CEO telling you to transfer money,” Zamir says.
“Generative AI will make it even easier for these messages to impersonate someone and target you as an individual, knowing what triggers you. I can build a very convincing email, with no links or attachments, that will convince you to transfer money to my account,” Zamir explains.
“Social-engineering attacks can only be stopped by advanced security solutions on email and other channels.”
Malware maliciousness
Passkeys don’t prevent malware, either.
Malware can enter your device when you open a document or other attachment in a message sent by a bad actor, or it can come through an app that you download to your phone after agreeing to grant it access to your data.
“The malware now owns your PC or device where your passkey is stored and I can continue to do actions in your name,” says Zamir. “I can impersonate you not by stealing your account credentials but by sitting on the device where you take your actions.”
Zamir recommends thinking twice before opening an attachment or tapping “agree” when an app asks permission to access your photos, contacts and documents.
“Security software can’t help with that. It’s more a matter of being aware that when you grant permissions to an app you downloaded, there’s nothing restricting them from taking everything from your phone and uploading it and potentially leaking it out,” he cautions.
“You must be careful to install only popular applications that are highly rated with many reviews, and avoid granting permissions. A photo app doesn’t need permission to access your contacts.”
The bottom line
To sum up, passkeys will make our digital dealings safer and easier, but we must still stay savvy to online dangers.
Zamir therefore recommends using passkeys whenever possible.
Right now, you can use a passkey to sign into Google, Apple or Microsoft, from which you can log into the majority of the apps you need, Zamir points out.
Although you will have the choice of continuing to use passwords if you wish, defaulting to passkeys for a password-free experience across all your devices, browsers and operating systems “will make your situation much better,” he concludes.