The Covid-19 pandemic has turned Israel’s world-respected cybersecurity professionals into frontline soldiers in a fight against what some see as a looming cyber pandemic.
Governments, companies, medical facilities and individuals are all potential victims of malware, identity theft and data stealing.
Earlier this month, Israel’s Ministry of Defense revealed what it called a successfully thwarted foreign cyber-attack targeting Israel’s defense industries.
Posing as managers, CEOs, HR officials and representatives of international companies, the would-be attackers built fake profiles on Linkedin and contacted employees in the defense industry with tempting job offers. In the process, they hoped to infiltrate the employees’ computers and gather sensitive security info.
Another major phenomenon keeping workers at Israel’s 436 cybersecurity companies busy is heightened vulnerability caused by remote work and education.
An April survey of 3,000 remote employees in the US, UK, France and Germany showed that work-from-home habits – including reusing passwords, accessing corporate systems on insecure “BYOD” devices and letting family members use corporate devices – are putting critical business systems and sensitive data at risk of hacking, according to CyberArk.
“The rate at which cyberattacks are taking place is increasing,” acknowledges Deborah Housen-Couriel, “but as time goes on we have better information on the direction, pattern and types of attacks.”
Housen-Couriel honed her legal expertise in the 1990s at Israel’s Ministry of Communications, which was then regulating the brand-new “plumbing” of cyberspace – antennas, microwave transmitters, undersea cables and satellites – that allows us to communicate digitally over the electromagnetic spectrum of radio waves.
Today, she is chief legal officer and VP-regulation for Tel Aviv-based Konfidas Digital cybersecurity and data protection consulting firm. She’s an advisory board member of the Federmann Cyber Security Research Center at Hebrew University, and teaches international and Israeli cyber law at several universities.
Housen-Couriel tells ISRAEL21c that the coronavirus situation has made many of us hyper-dependent on cyberspace for professional and personal pursuits – and therefore more vulnerable to “digital takedown.”
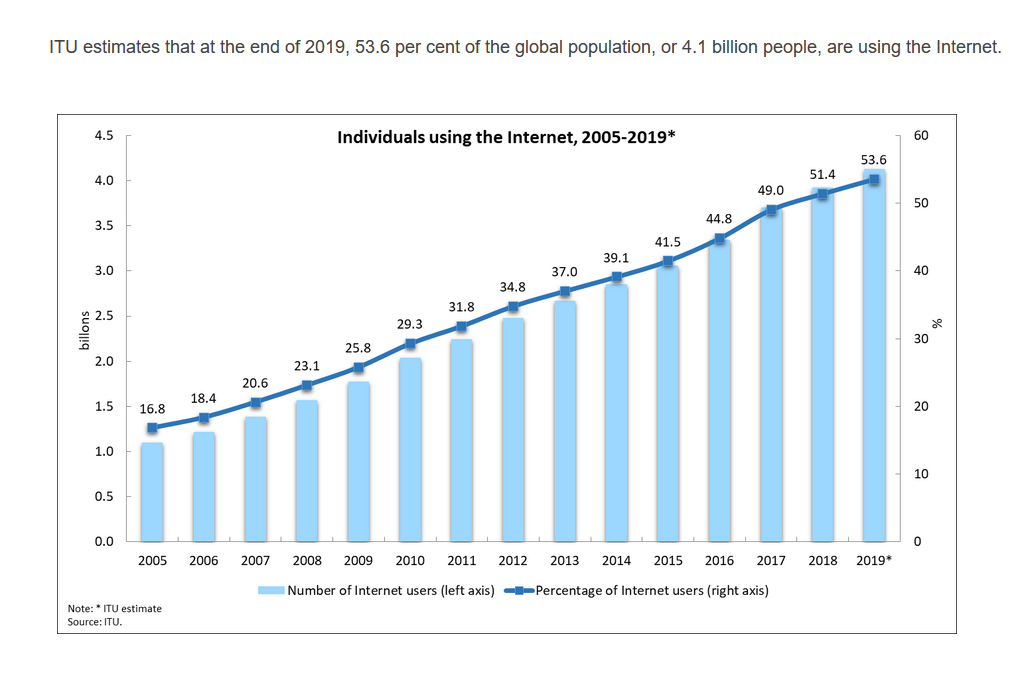
The International Telecommunication Union says estimates that more than half of humanity is online and vulnerable to cyberattack via cellphone or computer.
ISRAEL21c asked Housen-Couriel and three other cybersecurity industry leaders to explain what’s happening and what can be done to protect our identities, data and devices.
Lavi Lazarovitz, head of security research at CyberArk

We need not worry about a cyber pandemic, Lazarovitz says.
“It’s not that the attack potential got bigger; it just changed a bit,” he states.
“We do have organizations opening their perimeters and allowing employees to access services and apps remotely that before the Covid era were enclosed and protected.
“On the other hand, before Covid if an employee working from home got phished with a malicious link or malware, their laptop was inside the corporate network and the malware had room to move around and find the data, the crown jewels,” he explains.
During Covid, many workers are using their own laptops, “so now a simple phishing email may not be as detrimental because employees’ connections to the central organization are in many cases restricted.”
Lazarovitz says that CyberArk moved quickly to secure or reconfigure its tools and services for secure remote access as more people began working from home.
“We also adapted our research focus. We understood that video conferencing and messaging apps became the new medium for people to communicate, while email was the main medium for decades. We’ve seen in the last few months that attackers are trying to access those messaging apps to get internal information and credentials,” he says.
A prime example is the huge Twitter hack in July, believed to have resulted from attackers stealing credentials shared via Slack.
“We found that an external attacker could send a message to an employee who uses Microsoft Teams and it has a gif hosted on the attacker’s server. When the Microsoft Teams app goes out and tries to fetch this gif, behind the scenes the app authenticates to the remote server and shares with it the identity of the employee,” Lazarovitz says.
“Just by sending a gif, the attacker can hack an employee account and send messages to other employees, compromising their accounts. We worked closely with Microsoft to mitigate the problem and shared the details with the community on our blog posts.”
Lazarovitz says it was already apparent before Covid that the network firewall is no longer an effective perimeter.
“Because Covid pushed organizations to open services and apps externally, now the network perimeter cannot be relied on at all. The new perimeter is identity.”
To ensure that your work or private identity cannot be impersonated in front of services such as your bank account, Lazarovitz says to avoid sharing private information including your email address.
“Create a temporary email address for people or services you do not trust,” he counsels.
“Zero trust” is another concept that was emerging before Covid – especially after hackers compromised fingerprints and internal information on millions of US government employees in a 2015 cyberattack on the Department of Interior. CyberArk recently released a new zero-trust solution, Alero.
“Zero trust allows specific limited access to services, data and applications even if the employee or third-party vendor uses valid credentials,” Lazarovitz explains. “You get access only to what you need when you need it. You cannot trust anyone.”
Deborah Housen-Couriel, chief legal officer at Konfidas Digital

“Because of the Covid pandemic and its many demands for the sharing of our personal data, including our health data, we have to reevaluate our dependency on the digital world,” Housen-Couriel says.
“Maybe we’ve gone overboard in sharing personal data [online] without understanding what companies and governments are doing with it.” Data privacy protection is a rapidly developing area in many countries, including Israel.
“Not just personal data but also corporate data such as intellectual property and trade secrets are part of the cyber pandemic,” Housen-Couriel says. “Clients are often surprised to discover what assets they need to protect, and to carefully manage access to company data.”
Just as Konfidas provides clients with training exercises to be prepared in case of an attack, individuals should prepare an incident response plan, she suggests.
“If you’re hacked, you need to know which banks, social media and other digital platforms to inform immediately or to block.”
Housen-Couriel recommends a four-step process to protect yourself.
First, take stock of digital assets often targeted by hackers, including medical and financial records and ID numbers, as well as travel and other digital credits worth money.
Second, decide which of those assets you need or want to protect. Then, work out how to do that. A tailored cybersecurity service and cyber insurance for businesses can also be made to fit individual or family cyber needs.
The final step is paying attention to changes in data-protection and cyber-protection regulations.
For example, the Court of Justice of the European Union recently ruled that the Irish data protection commissioner violated an Austrian citizen’s rights under the EU’s General Data Protection Regulation (GDPR) by transferring his Facebook data to servers in the United States.
Although our hyper-connectivity has enhanced our ability to cope with the corona pandemic and keep up to date, it is also “a wakeup call to how vulnerable we are, not just as biological animals but also in terms of our digital identities,” Housen-Couriel says. “They’re being taken advantage of now and will continue to be.”
And, she points out, “There is no such thing as a cyberattack vaccine.”
Emmanuel Benzaquen, CEO of Checkmarx

“What Covid has done, with everybody working from home, is increased exponentially the attack surface and expanded the opportunities for vulnerabilities to be exploited,” Benzaquen tells ISRAEL21c.
“Before, attacking an organization meant finding the main firewalls and entry points. When there are tens of thousands of home offices, you have to make sure everybody’s behind the right attack surface so that you don’t create another exposure.”
The pandemic hit Israel in March, around the same time Checkmarx was acquired by global private equity firm Hellman & Friedman at a valuation of $1.15 billion.
Checkmarx specializes in application security. More than 40 of the Fortune 100 use its products to mitigate risk, secure code, and embed security into their software development.
“Application security is a fairly new cybersecurity layer now that everything is controlled by apps,” Benzaquen explains.
Checkmarx makes products that find vulnerabilities, enable app developers to be more security aware and keep cloud data safe.
“The digital transformation, together with Covid, has put the cloud on steroids,” Benzaquen says. “Our cloud solution product enables small and medium businesses to access application security in a click-and-scan approach. We’ll launch more of these over the coming months.”
Benzaquen sees an increase in phishing attacks, often disguised as emails inviting people to a WebX or Zoom meeting.
“You have to be very careful not to share your information because we’re dealing with a much bigger capacity of email and Zoom invites. Just because a website looks legit doesn’t mean it is.”
He also says to be vigilant about installing smartphone apps that ask permission for access to your database, pictures and audio.
“In the future, maybe in another generation, there won’t be any piece of software developed without being securely scanned and verified. That’s the direction we need to go in.”
Motti Sorani, CTO of CyberMDX

CyberMDX provides cyber-intelligence products that enable hospitals and other healthcare-delivery organizations to secure and manage their connected medical devices.
The Tel Aviv-based company’s research finds that one in six US data breaches occurs in hospitals, and 61% of medical devices are at persistent cybersecurity risk.
On-premises connected medical devices, says Sorani, are “extremely vulnerable” to being hacked or held for ransom.
“Some were built without security in mind, some suffer from broken post-market security processes. Now, they are exposed to a much higher risk, as the chances an intruder will get into the network became higher.”
Covid-19 didn’t change the way CyberMDX prepares healthcare-delivery organizations to strengthen “cyber-hygiene,” Sorani says, but the pandemic “actually validates it in a way we did not even imagine when we built our solution.”
The company discovered that its product was able to help organizations potentially reduce risk of exposure.
“One of our customers in New Jersey, which until recently was the second most impacted US state by the pandemic, used our solution to help minimize staff exposure to the virus,” he explains.
“They recognized that staff would frequently search for Covid-19 related equipment – for instance, IV pumps and/or ventilators — potentially exposing them to infected patients in different rooms. They can now use the CyberMDX solution to locate these devices, know when they were being used, and do this all without having to search in the rooms of infected patients.”
Sorani says CyberMDX customers “are seeing the life-threatening impacts of Covid first-hand. When you add in additional exposures to data breaches and ransomware, they cannot afford to be distracted. A robust cybersecurity program needs to be there.”

















