‘Yikes’ is the first thought that comes to mind upon reading a new study by researchers at the Ben-Gurion University of the Negev (BGU) Cyber Security Research Center.
The researchers have demonstrated that data can be stolen from an isolated “air-gapped” computer’s hard drive reading the pulses of light on the LED drive using various types of cameras and light sensors.
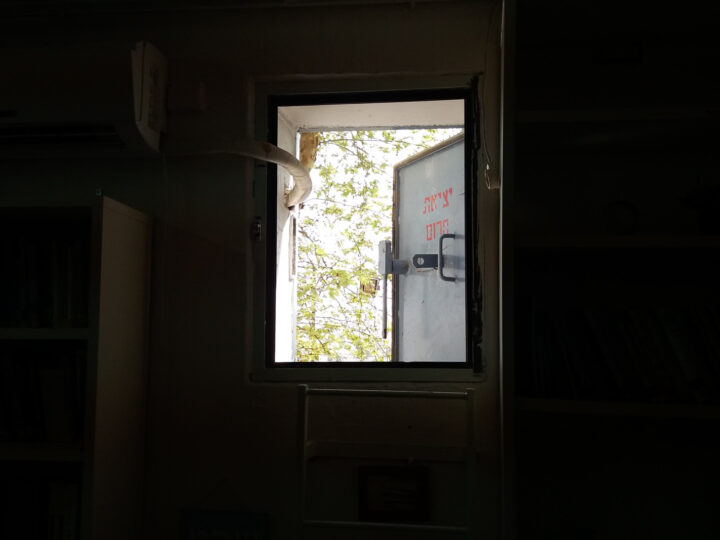
In the new paper, the researchers show how data can be received by a quadcopter drone flight, even outside a window with line-of-sight of the transmitting computer.
Dr. Mordechai Guri, head of R&D at the Cyber Security Research Center, explains that air-gapped computers are isolated — separated both logically and physically from public networks — ostensibly so that they cannot be hacked over the Internet or within company networks.
But Guri – together with BGU researchers Boris Zadov, who received his M.Sc. degree from the BGU Department of Electrical and Computer Engineering and Prof. Yuval Elovici, director of the BGU Cyber Security Research Center– have made it one of their missions to do exactly that: hack air-gapped computers.
In the latest project, the research team utilized the hard drive (HDD) activity LED lights that are found on most desktop PCs and laptops. The researchers found that once malware is on a computer, it can indirectly control the HDD LED, turning it on and off rapidly (thousands of flickers per second) – a rate that exceeds the human visual perception capabilities. As a result, highly sensitive information can be encoded and leaked over the fast LED signals, which are received and recorded by remote cameras or light sensors.
“Our method compared to other LED exfiltration is unique, because it is also covert,” Guri says. “The hard drive LED flickers frequently, and therefore the user won’t be suspicious about changes in its activity.”
Air-gapped computers typically contain an organization’s most sensitive and confidential information.
The BGU cyber team has conducted a number of studies to demonstrate how malware can infiltrate air-gapped computers and transmit data.